See the full findings
Download the 2026 IP Intelligence Study to learn how security teams use IP intelligence to detect threats, reduce false positives, and speed investigations.
Get your copy
For years, security teams have relied on the idea that most malicious traffic could be identified and filtered out. Suspicious IPs stood out. Bad actors were, if not obvious, at least detectable with the right signals.
That assumption no longer holds.
Today’s attackers are deliberately blending in. They route activity through anonymizing VPNs and residential proxy networks that make malicious traffic look indistinguishable from legitimate users. This has created new challenges for security, threat hunting, and fraud teams.
According to our newly released 2026 IP Intelligence Study:
What do these findings mean? Using obfuscated IPs isn’t rare or sophisticated behavior anymore – it’s standard operating procedure. Attackers aren’t breaking in through obvious gaps. They’re logging in through the front door, and the consequences are significant.
This post summarizes the findings from the Spur 2026 IP Intelligence Study and offers guidance to align your organization with evolving defensive strategies.
Download the 2026 IP Intelligence Study to learn how security teams use IP intelligence to detect threats, reduce false positives, and speed investigations.
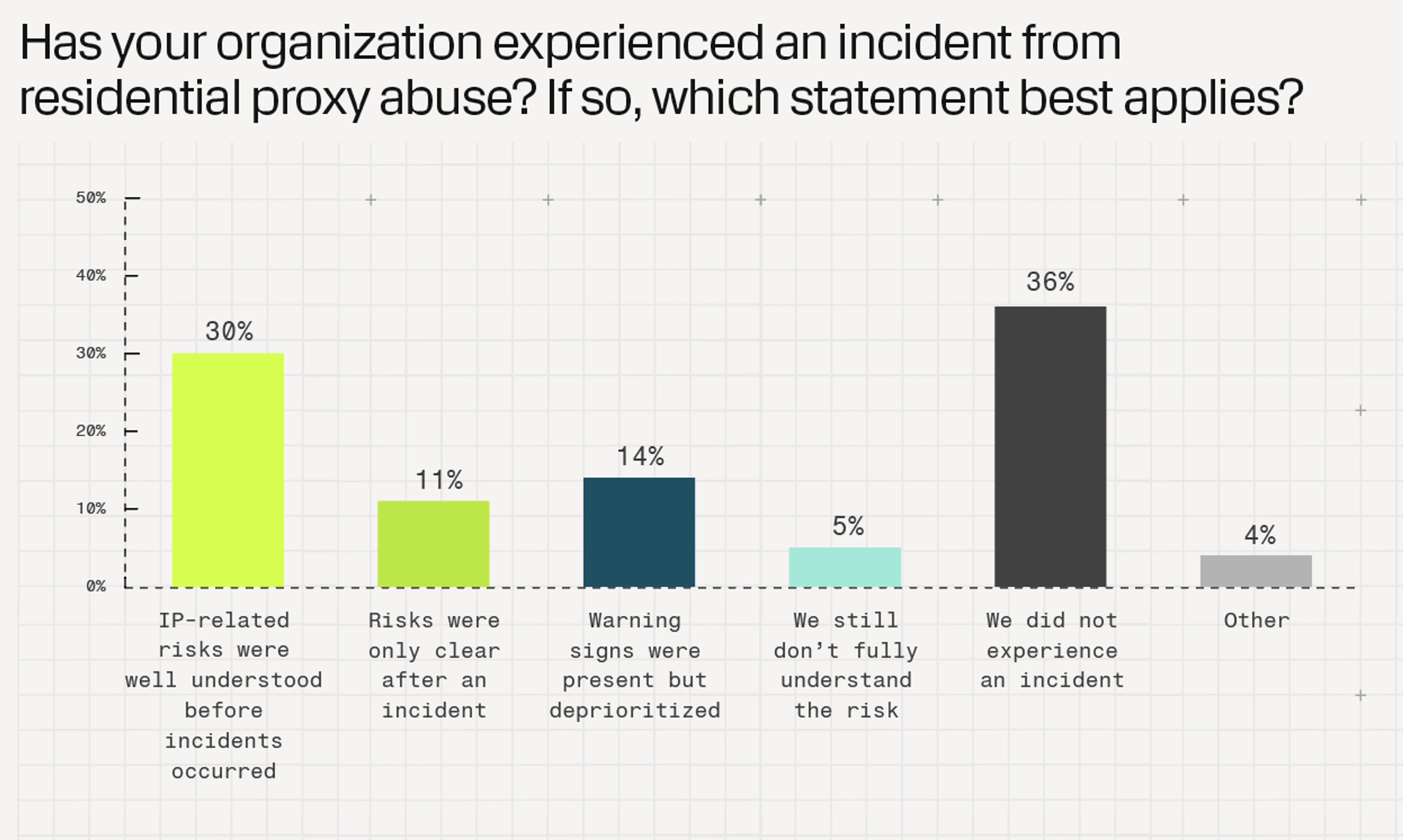
Get your copyOnly about a third of respondents said they truly understood residential proxy abuse risks before an incident occurred, and a similar percentage feel confident they can fully monitor IP-based access paths into their environment. That gap – between knowing there’s a problem and being able to act on it – is where many security programs get stuck. It’s not a visibility issue in the traditional sense since the data and alerts exist. But the ability to interpret and act on that information in real time is still missing.
Part of the problem is how IP intelligence is actually used. In most organizations, it remains a reactive tool. Analysts enrich logs, investigate incidents, and block traffic after something has already gone wrong. These are necessary workflows, but they’re fundamentally backward-looking.
At the same time, expectations are shifting. Many teams want IP intelligence to play a much bigger role, such as informing decisions earlier in the process, enabling automation, and helping systems respond dynamically rather than manually. In fact, about half of respondents say they want IP intelligence to support predictive decision-making and automated enforcement.
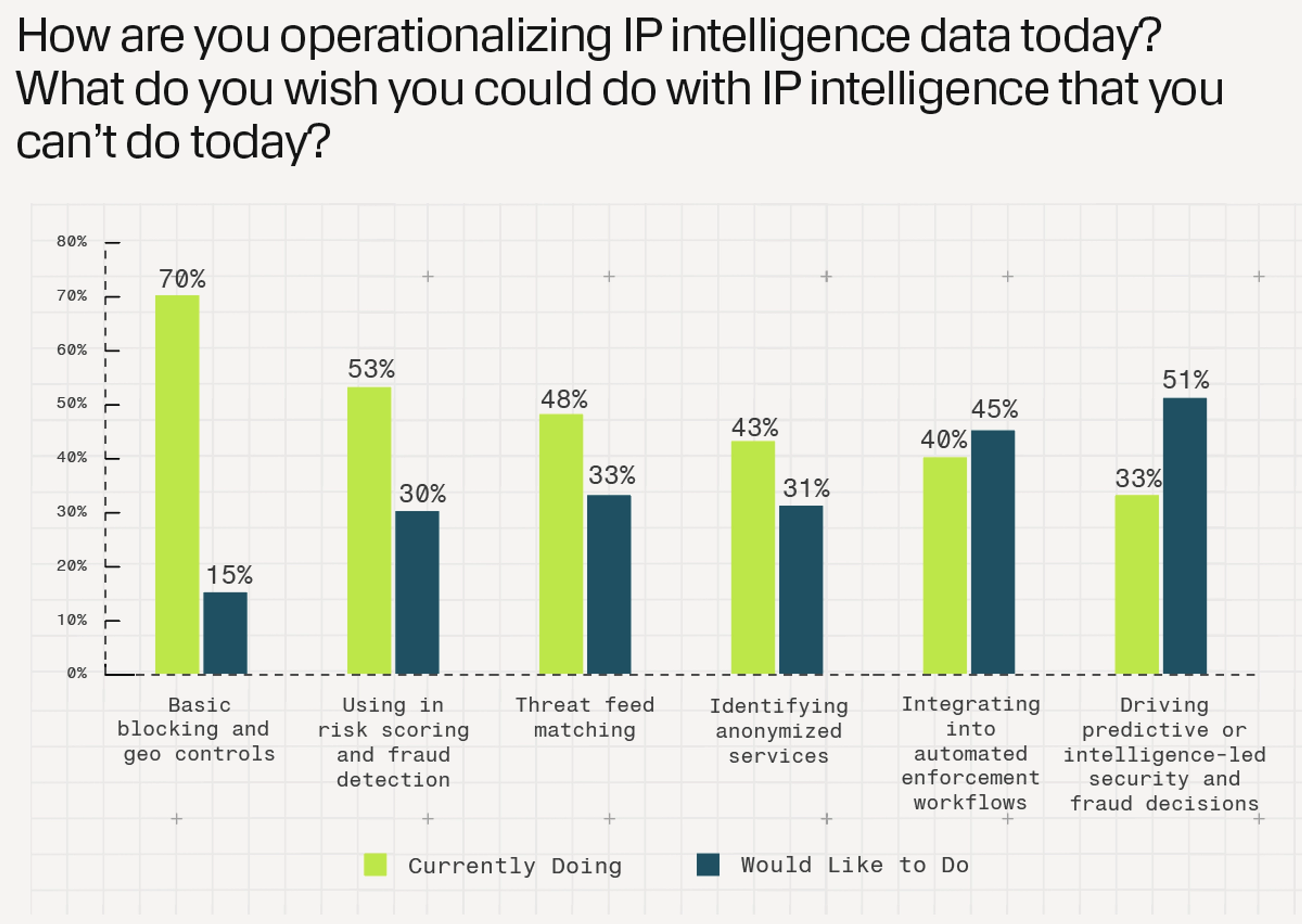
There’s a clear mismatch here. The technology is being used for investigation, but the real demand is for decisioning.
One of the most interesting findings in the research points to a growing blind spot: internal LAN exposure. While much of the focus on malicious IPs is on external threats, many organizations have limited visibility into proxy usage on employee devices, especially in environments with remote work or BYOD policies. Even more striking, a majority of respondents aren’t strongly concerned about the potential exposure this creates.
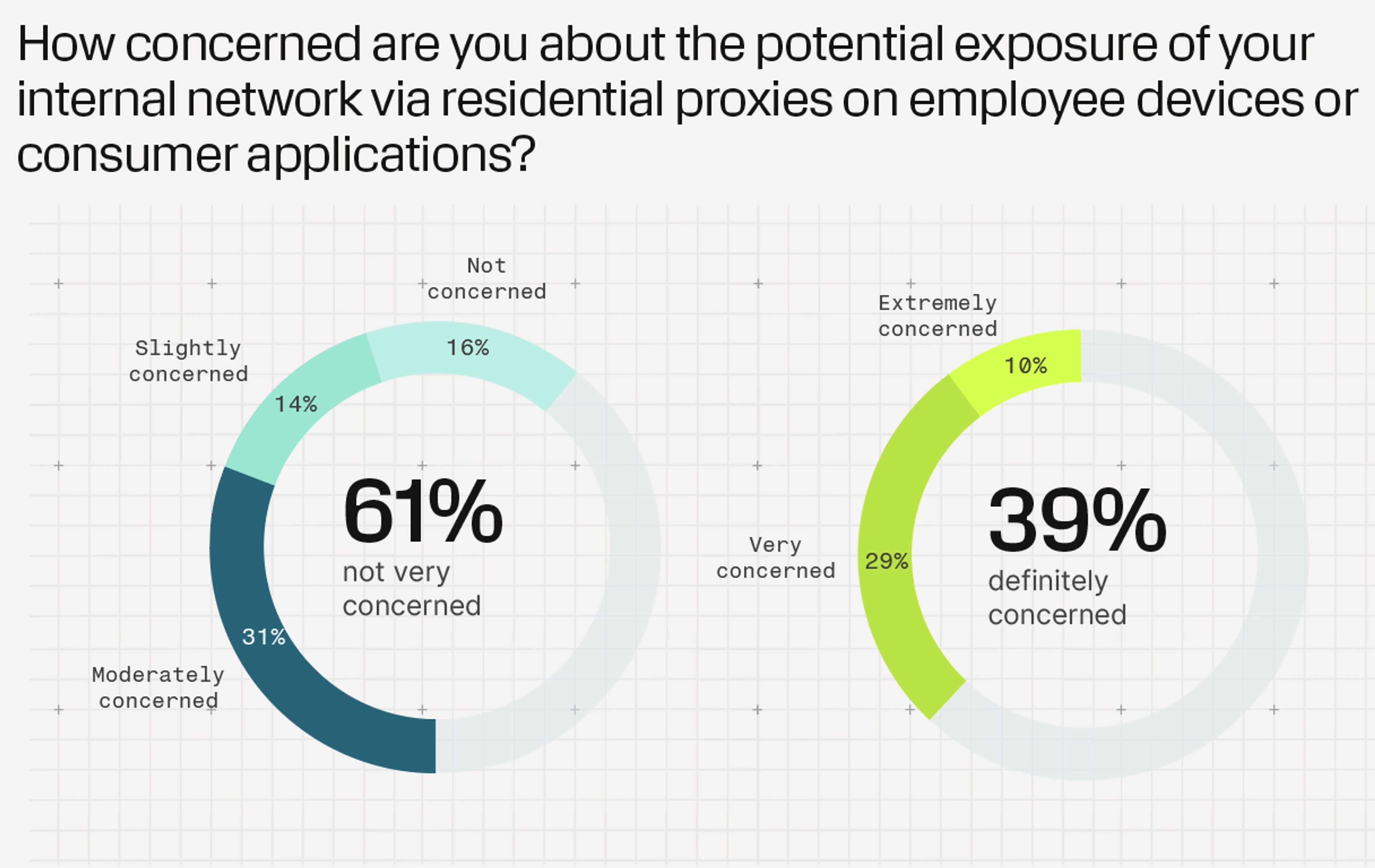
That lack of concern is shocking. When anonymizing infrastructure operates inside the network boundary, it challenges one of the oldest assumptions in security – that internal traffic is inherently more trustworthy. In reality, proxy-enabled devices can provide attackers with a foothold that looks legitimate from the inside out.
When we asked teams about their biggest challenge with IP intelligence, the answer wasn’t coverage or cost. It was context. Nearly half of respondents said they struggle to understand the “who” and “why” behind an IP address.
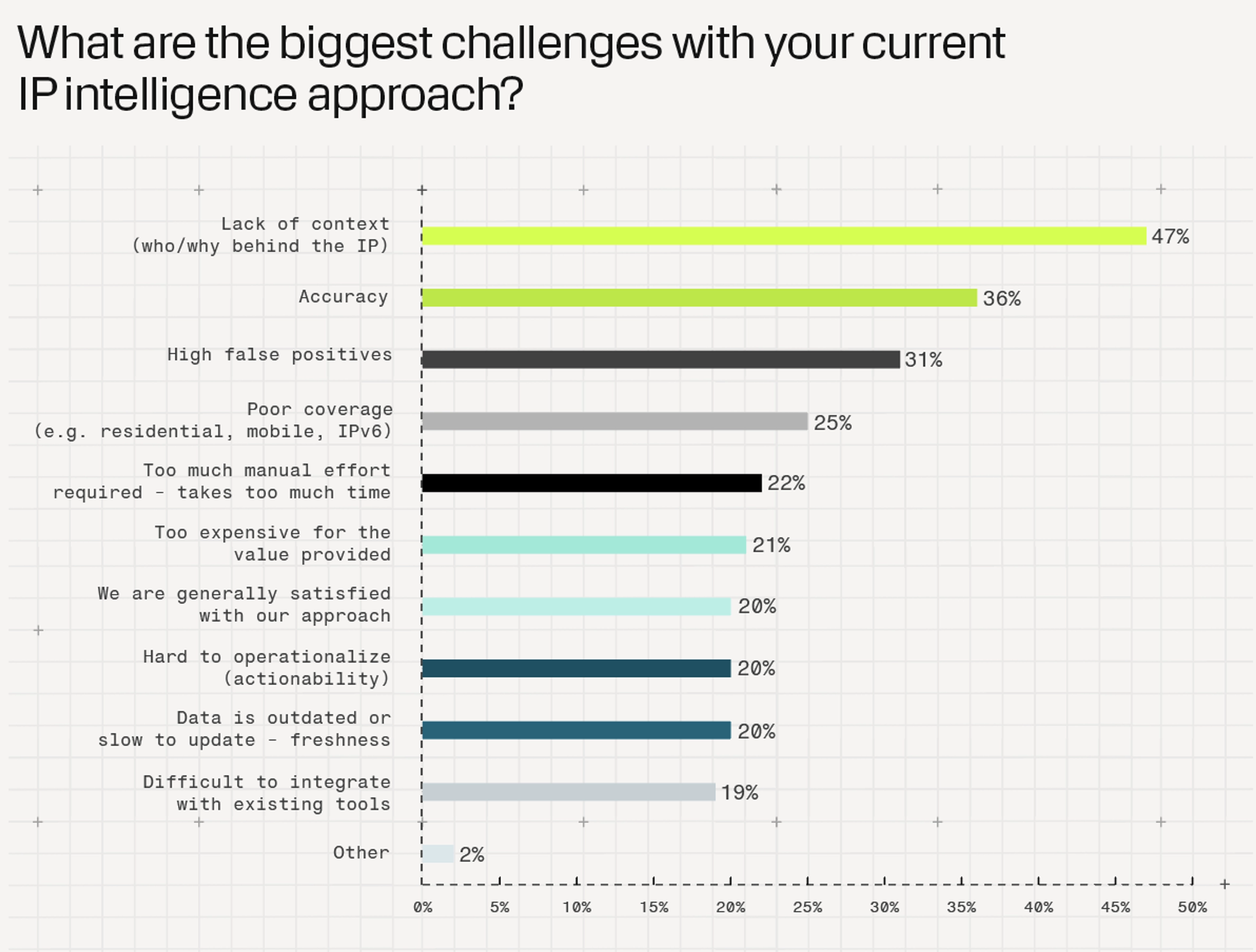
That missing layer of meaning forces analysts into manual workflows, piecing together clues across multiple tools just to answer basic questions. The result is slower investigations, higher false positives, and a growing operational burden. Even with abundant data, teams are left making decisions with incomplete information.
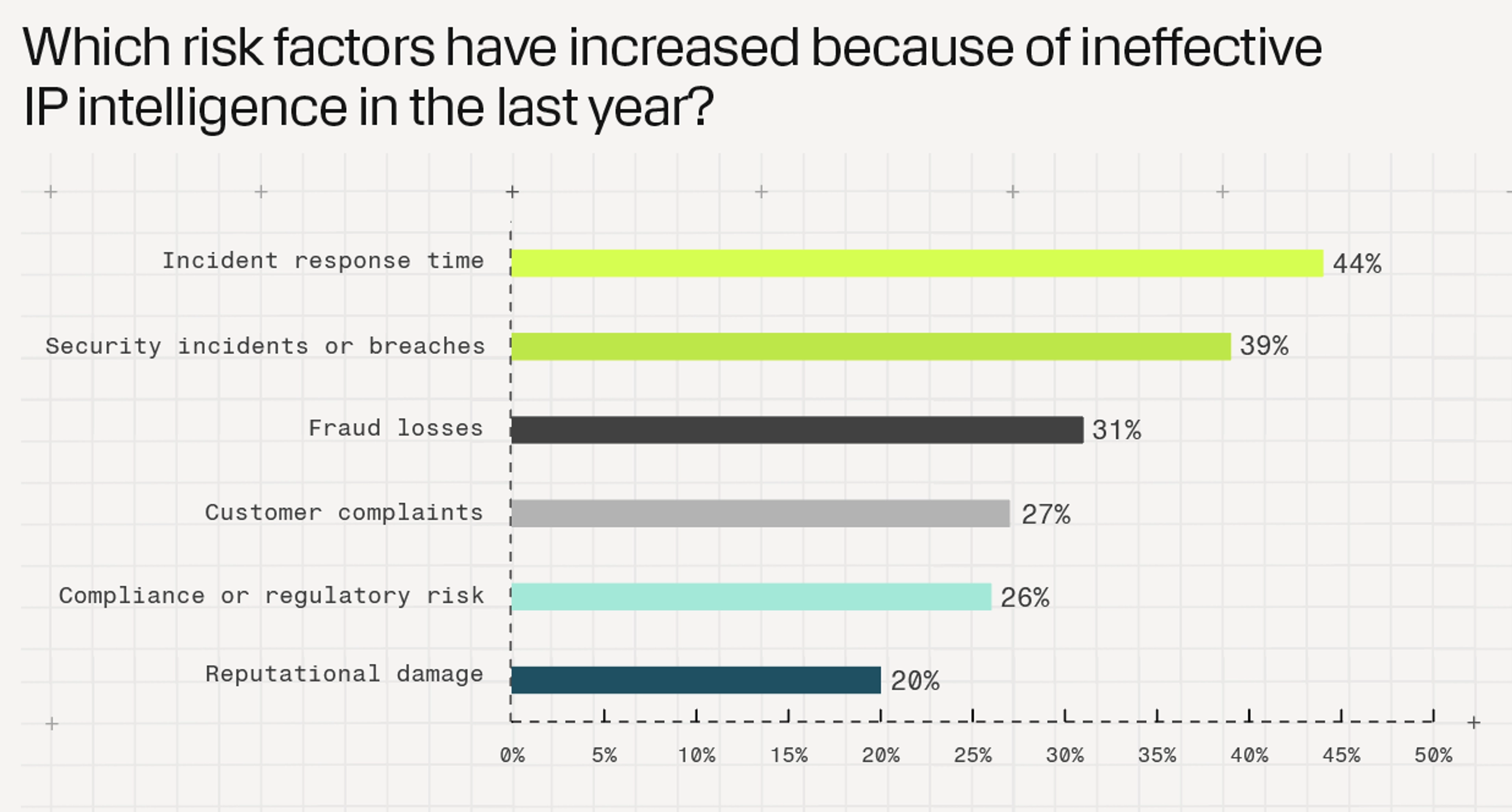
A surprising 34% of respondents are not measuring the effectiveness of their current IP intelligence efforts at all, despite acknowledging risk factors such as incident response time and security incidents or breaches increasing as a result of ineffective IP intelligence. Respondents are clear that investigation time and false positive improvements would benefit their teams most.
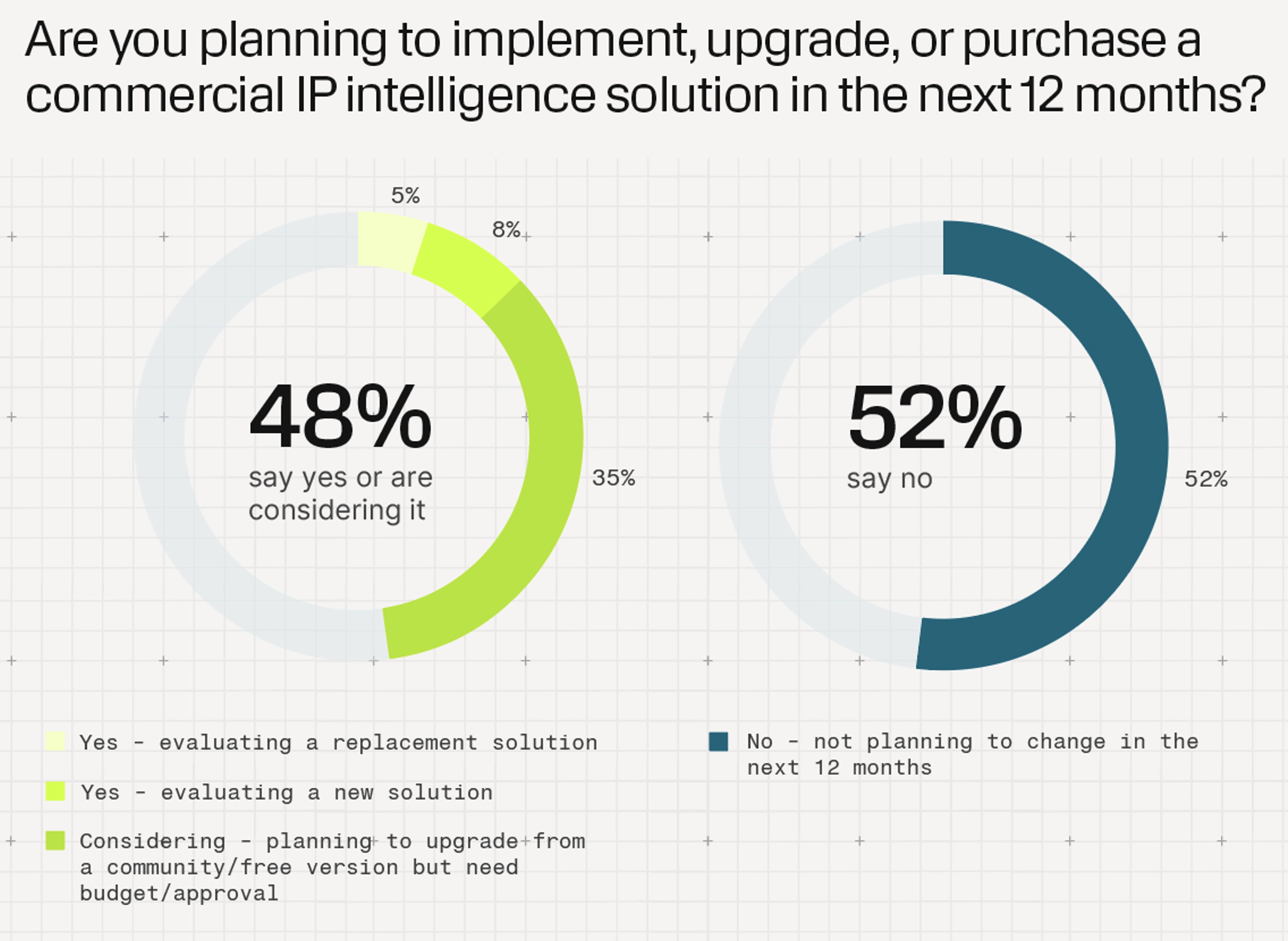
Despite the challenges, there’s a clear sense that change is coming. Many organizations are actively evaluating new approaches to IP intelligence, with nearly half planning to upgrade or replace their solutions in the next year, despite budgetary challenges. What they’re looking for isn’t just better data feeds, but fundamentally different capabilities: richer context, stronger automation, and the ability to act on signals in real time.
This marks an inflection point. IP intelligence is evolving from a supporting tool into a core part of how security decisions are made.
The organizations that are moving ahead aren’t necessarily the ones with the most data. They’re the ones changing how that data is used. They’re:
None of this requires a complete reinvention of security infrastructure. But it does require a mindset shift.
For years, IP data been treated as a way to explain what already happened. But the next phase is about using it to influence what happens next. When attackers are hiding in plain sight, the advantage no longer comes from having more signals. It comes from turning those signals into decisions quickly, confidently, and at scale.
That’s the real gap. And it’s where the opportunity lies.
The full Spur 2026 IP Intelligence Study breaks down how more than 200 security practitioners are actually using IP intelligence today, where they’re struggling, what’s changing, and where leading teams are pulling ahead.
If you’re evaluating your own approach to IP intelligence, the data offers a clear benchmark:
Download the full study to explore all findings, charts, and recommendations.
Ready to experience our high-fidelity IP intelligence in action? Start with free access to Spur Community or schedule a 1:1 demo to discuss your specific requirements with a Spur representative.
Start enriching IPs with Spur to reveal the residential proxies, VPNs, and bots hiding in plain sight.