Spur IP Geo: Next-Generation IP Geolocation for Security and Compliance Now Generally Available

In March 2025, we introduced IP Geo in beta — a next-generation approach to IP geolocation designed to bring security teams higher accuracy, integrity, and usability than legacy datasets could deliver.
Today, we’re excited to announce that Spur IP Geo is now generally available! After months of real-world testing with customers across industries, IP Geo is ready and available to integrate into Spur’s data feeds, enabling organizations worldwide to improve fraud detection, threat hunting, and compliance operations.
Why IP Geo vs. Legacy Tools?
Traditional IP geolocation tools often rely on outdated databases, self-reported information, or unverifiable corrections from users and providers. This introduces blind spots and inaccuracies that attackers exploit to mask their true geographic presence.
Spur IP Geo changes this by grounding location intelligence in technical analysis and verified data, eliminating dependence on crowdsourced corrections. With all routable IPv4 space included and 99.7% city-level coverage, IP Geo provides the most comprehensive and trustworthy IP enrichment baseline available.
Key Capabilities
- Comprehensive Coverage: IP Geo delivers all IPv4 network space enriched with proprietary data, updated weekly.
- Validated Accuracy: Beta customer testing has shown an industry-leading 99.7% city-level precision, exceeding legacy tools.
- Highest Data Integrity: Every result is grounded in hard network evidence by verifying a user’s point of presence without self-validation.
- Privacy by Design: Locations are mapped to ~2 million global hexagons to prevent over-precision that could identify individuals.
- Security-First Design: Nearby IPs are mapped into grid cells for simplified, high-fidelity enrichment.
- Seamless Integration: IP Geo is available to integrate with your Spur Data Feeds or plug into your existing analytical pipelines.
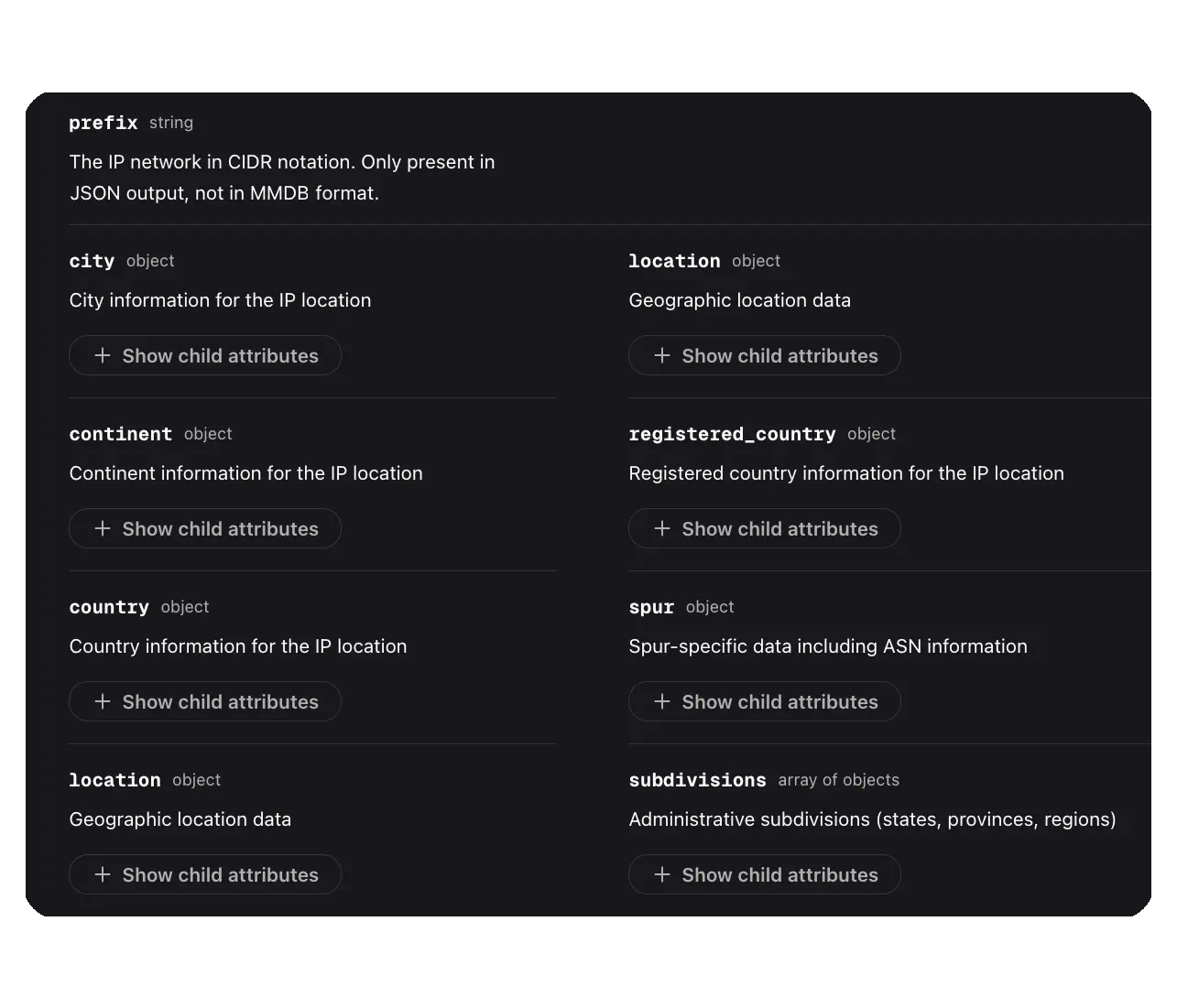
Spur IP Geo delivers high-fidelity internet-wide geographic enrichment covering all possible IPv4 addresses across 200+ countries.
How to Use IP Geo
Customers leverage IP Geo to:
- Quickly identify whether suspicious traffic is truly local or being spoofed.
- Accurately verify user location against claimed activity, reducing false positives.
- Confidently enforce policies based on accurate country- and city-level data, aiding in security and compliance.
Get Started With IP Geo
Spur is committed to delivering the highest-fidelity IP intelligence in the world. With IP Geo now generally available, organizations can depend on IP geolocation that is accurate, privacy-conscious, and designed for security.
The best way to understand how improved geolocation data can improve your security, threat hunting, and fraud prevention is to see it in action. Spur offers a free community version that enables you to explore anonymizer detection, infrastructure classification, and more. When you are ready, request a demo.
See the Difference Between Raw Data & Real Intelligence
Start enriching IPs with Spur to reveal the residential proxies, VPNs, and bots hiding in plain sight.